I ran across this great article on Codetapper’s C64 site and wanted to share the link.

There was a quote from Chuck Sommerville about how great the copy protection was on California Games (it was Vorpal)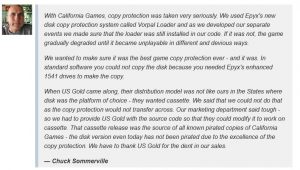 .
.
The article does a great job debunking the claim that all cracked versions of Summer Games came from the US Gold Cassette release.
Talking to crackers from Eagle Soft Incorporated
When I downloaded games from BBS’s back in the day here in the USA, Eagle Soft was the most common cracking group, from the games I grabbed. But here is the link to this great article: https://codetapper.com/c64/rants/california-games-c64-copy-protection/
This is a must and great read! Thank you Codetapper.